Guardians at the Gate: How Emerging Start-Ups Are Racing to Expose AI-Generated Deception
The telephone connection crackled as a daughter greeted her parents in Spanish from thousands of miles away. Something, however, felt off. The cadence was familiar, and the tonal rises mimicked their child’s voice, yet a robotic stiffness lingered between syllables. Within moments her father asked the question every deepfake researcher both dreads and longs to hear: “¿Eres tú de verdad?”—is it really you?
The voice on the line was not. It had been synthesized by Reality Defender, one of several new companies building artificial intelligence designed to identify, and in this case fabricate, deceptive media. For the experiment, the journalist supplied nine seconds of archival audio plus years of social-media posts in both English and Spanish. Reality Defender’s system fine-tuned pitch, stability, and resonance until a passable clone emerged—good enough to fool a casual listener, though not yet resilient against the scrutiny of loved ones. The brief trial, conducted with permission, illustrates the paradox these start-ups confront every day: in order to expose deepfakes, they first have to learn how to produce them.
A Market Built on Mistrust
Manipulated images and audio are older than radio, but today’s synthetic media requires only a web browser and a few minutes of processing time. By 2023, the World Economic Forum estimated the global market for deepfake detection tools at roughly $5.5 billion. Investors are betting that the same breakthroughs enabling realistic voice cloning and AI-generated video will turbo-charge demand for corporate verification tools, just as the explosion of computer viruses in the 1990s birthed the antivirus industry.
Reality Defender, Pindrop, and GetReal approach the challenge in similar ways. Each platform trains large machine-learning models on paired datasets: genuine clips annotated as “real” and synthetic clips labeled “fake.” Over millions of iterations, the models learn to surface microscopic inconsistencies—imperceptible variances in background noise, pixel shading, or phrase timing—that betray an algorithm’s handiwork. “We’re teaching the machine to notice what the human ear can’t,” explains Alex Lisle, Reality Defender’s chief technology officer. “Every time a generative model improves, we feed its output back into our detector. It’s a continual arms race.”
From Executive Impersonation to Assembly-Line Fraud
Until recently, most deepfake scams focused on high-value targets. Attackers would clone a chief executive’s voice and instruct accounting staff to transfer funds, or forge a politician’s likeness to depress voter turnout. But access to open-source voice models and user-friendly video tools has broadened the risk surface dramatically. Lisle describes a recent incident at a publicly traded firm where criminals harvested every employee’s name from LinkedIn, scraped TikTok and Facebook for sample speech, and generated tailored voiceprints. “Instead of aiming at one manager, they robocalled the whole company simultaneously,” he says. “If even one person complied, the payout dwarfed their costs.”
The consequences are already measurable. A 2024 industry survey found the average corporate loss per deepfake event was $450,000, with several organizations reporting single-incident damages exceeding $1 million. Pindrop’s chief product officer Nicholas Holland notes that even his own company has faced synthetic intruders. “We’ve interviewed applicants who sailed through hiring, then referred ‘colleagues’ that turned out to be themselves operating multiple identities—different voices, new faces, separate Slack accounts,” he says. “In effect, one person landed three salaries.”
Speed Versus Fidelity
Deepfake detectors require near-instant decisions. A bank cannot place a wire transfer on hold for fifteen minutes while back-office algorithms analyze tone texture. Yet generative models excel when granted generous processing cycles. The journalist’s Spanish clone, for example, could respond in real time only by sacrificing realism. When the team switched to text-to-speech and allowed longer rendering, the output became chillingly lifelike; at conversational speed it stuttered, inserted filler, and mis-timed pauses, enough for family members to sense the oddness.
Balancing these constraints is central to commercial adoption. “The trade-off triangle is speed, accuracy, and cost,” Holland explains. “You want all three, but you can’t max each simultaneously on current hardware.” Corporate customers generally accept a small false-positive rate so long as urgent calls—think emergency wire recalls or authentication during merger negotiations—complete without delay. That tolerance drops sharply when the end user is a private individual fielding a panicked phone call that might be an extortion attempt.
Why Consumers Remain Exposed
Despite headline-grabbing kidnappings hoaxes and ransom schemes, consumer-grade protection remains rare. Start-ups argue that individuals often underestimate the threat, making it difficult to charge for software they do not believe they need. Instead, Reality Defender and Pindrop concentrate on enterprise clients—banks, insurers, video-conferencing providers—under the logic that everyone benefits when the gatekeepers integrate defenses directly into communication platforms.
Scott Steinhardt, Reality Defender’s head of communications, likens the emerging model to modern antivirus. “Most people stopped buying boxed virus scanners because browsers, email providers, and operating systems now do the scanning upstream,” he says. “Deepfake detection should become just as invisible. The content is vetted before it ever reaches your phone.”
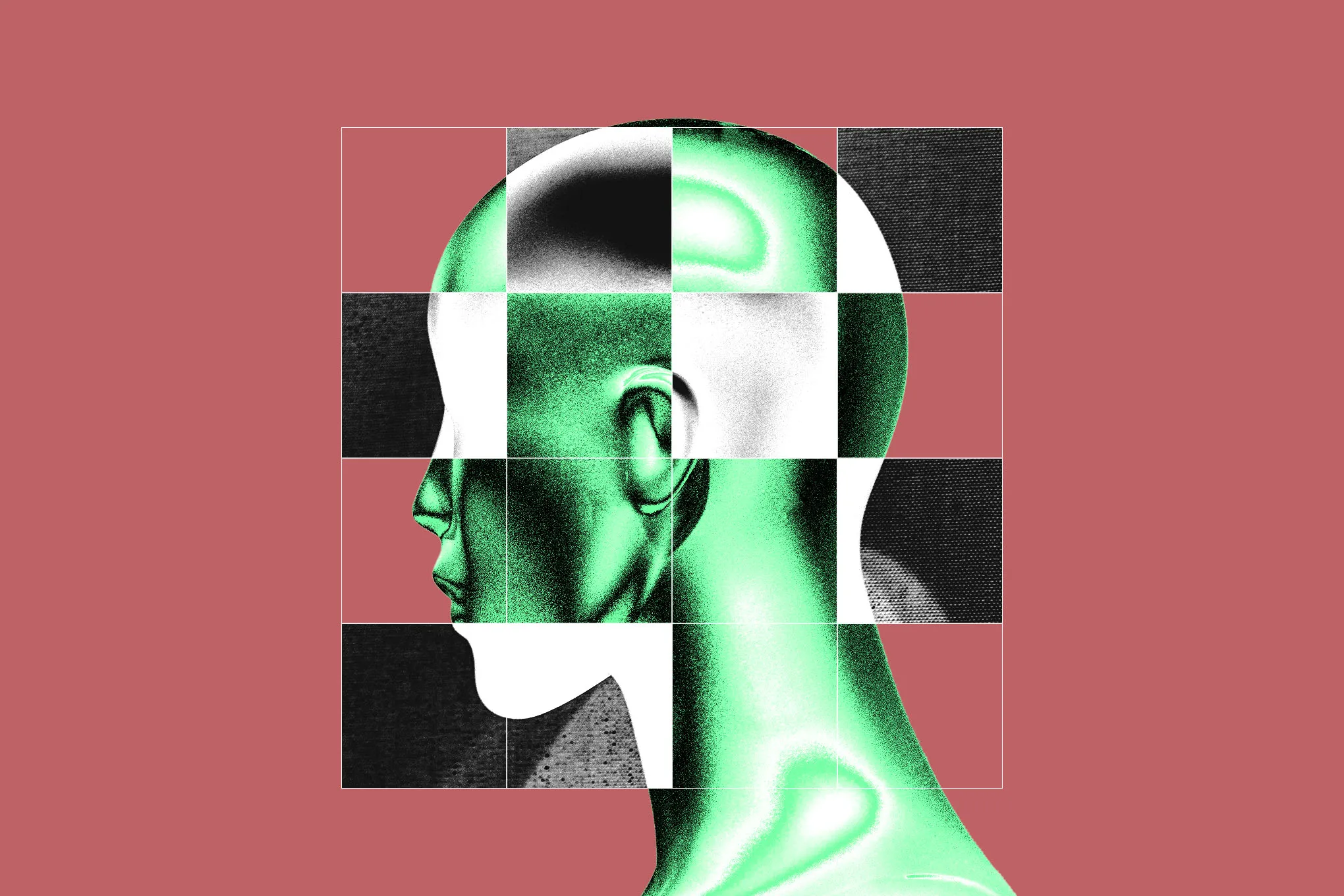
Imagem: Cath Virginia
Pindrop is leaving the door open for a standalone consumer product but admits the technical bar is high. Not only must the system flag suspicious audio in seconds, it must do so on smartphones with limited battery and ensure user privacy amid tight biometric regulations. “If we’re storing face and voice prints, we have to guarantee deletion schedules and secure encryption,” Holland says. “Trust evaporates the instant someone learns their mother’s plea for help was actually a training sample.”
Illusion Meets Ethics
The journalist who attempted to fool her parents ultimately called off a harsher test scenario involving simulated abduction screams. The potential trauma—and the possibility of inadvertently violating federal wire-fraud statues—proved too great. Instead, she tried an English-language version on her brother. His immediate response: “Oh, no.” Family ties once again triumphed over synthetic cadence.
Yet the exercise underscores a chilling reality: relational familiarity is rapidly becoming the final line of defense. For high-stakes interactions with strangers—human-resources video interviews, customer-service helplines, disaster-relief donations—that shield is absent. Without automated screening, even a marginally convincing deepfake can weaponize empathy, fear, or urgency before skepticism kicks in.
Lisle is blunt about the evolutionary pressure. “In cybersecurity we talk about trust boundaries. For forty thousand years, sight and sound formed an implicit boundary—we believe what we perceive. Deepfakes puncture that wall. Now every transaction needs an extra layer of proof, and attackers search for the gaps.”
The Road Ahead
Advances in generative AI show no sign of slowing. New diffusion models generate photorealistic hands and teeth, historically glaring giveaways. Voice engines modulate emotional nuance that once betrayed computer origins. Meanwhile, detection companies incorporate the latest fakes into training pipelines, closing yesterday’s loopholes while tomorrow’s open.
The outcome remains uncertain, but precedent suggests a cyclical détente. Spam email exploded in the early 2000s until filters, authentication protocols, and legal crackdowns rendered most inboxes usable again. Phishing still exists, yet the casual user rarely sees the worst of it. A similar equilibrium could arise for synthetic media: pervasive background scanning paired with digital-signature frameworks verifying authentic content.
In the interim, vigilance matters. Financial institutions increasingly deploy voiceprint authentication only alongside step-up factors such as device fingerprinting and behavioral analytics. Video-conference platforms experiment with on-screen watermarks indicating verified feed sources. And families, armed with healthy skepticism, devise simple pass-phrases or code words to validate urgent requests.
The next time a voice that sounds like your daughter calls from an unfamiliar number, you may ask for the family recipe she alone knows, or the name of the dog’s first vet. A stutter or blank pause might buy precious seconds—long enough for detection algorithms humming in a server farm to label the stream as synthetic and cut the connection. In an era where seeing and hearing is no longer believing, verification is everyone’s responsibility, assisted by rapidly evolving tech sentinels on the digital frontier.
FAQ
- What is a deepfake?
A deepfake is audio, video, or imagery generated or manipulated using deep-learning algorithms to convincingly mimic real people or events. - Why are deepfakes dangerous?
They can be used for fraud, political misinformation, non-consensual pornography, identity theft, and emotional extortion scams. - How do detection companies identify deepfakes?
They train AI models on large datasets of confirmed real and fake media, teaching the system to spot subtle anomalies in sound waves, pixel patterns, or timing. - Can individuals buy deepfake detection software?
At present, most tools target enterprise clients such as banks and telecom providers. Consumer options are limited but may emerge as demand grows. - What can I do to protect myself right now?
Use multi-factor authentication for sensitive accounts, verify unexpected requests through a secondary channel, and be cautious of urgent appeals involving money or personal data.